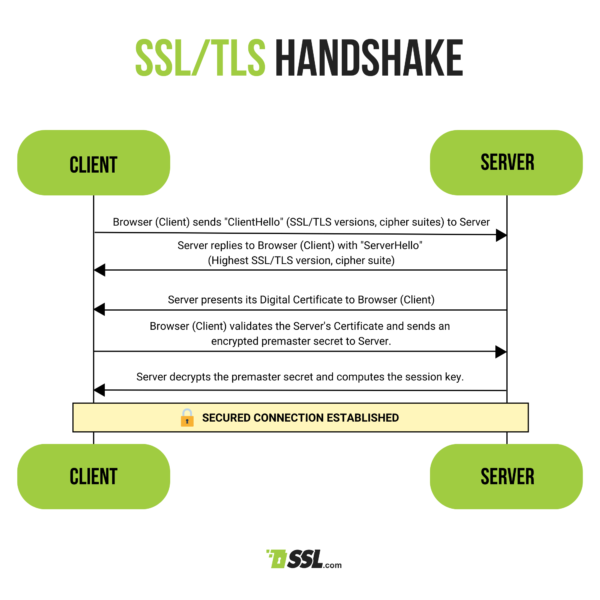
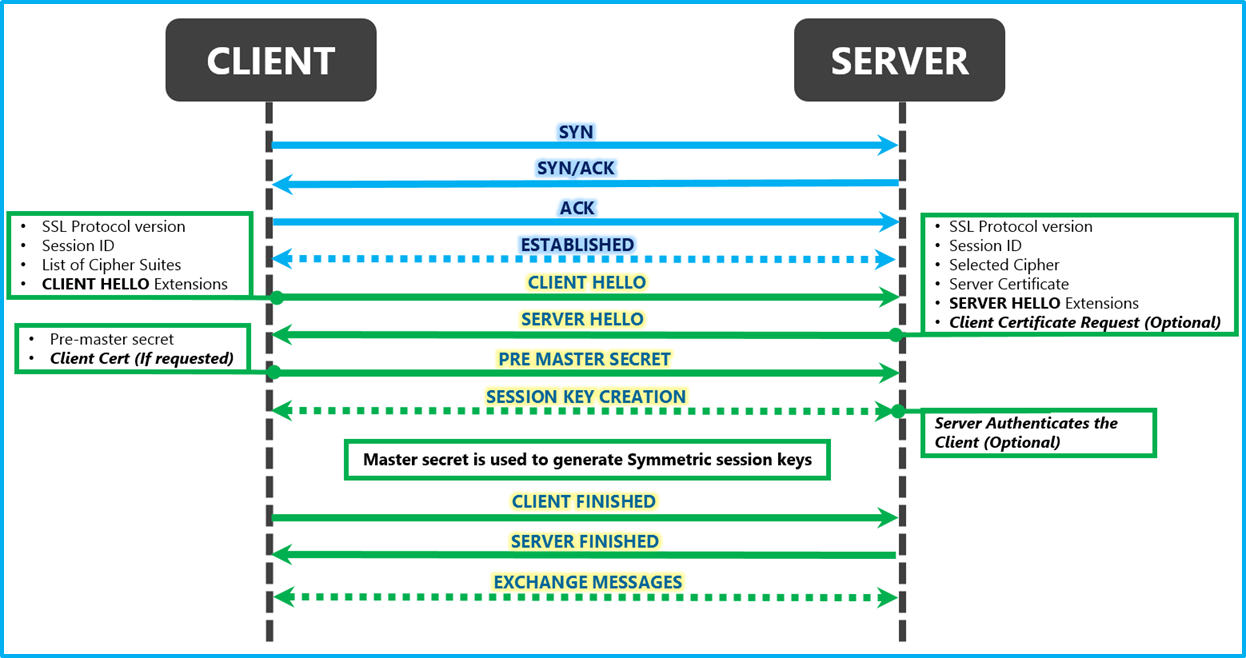
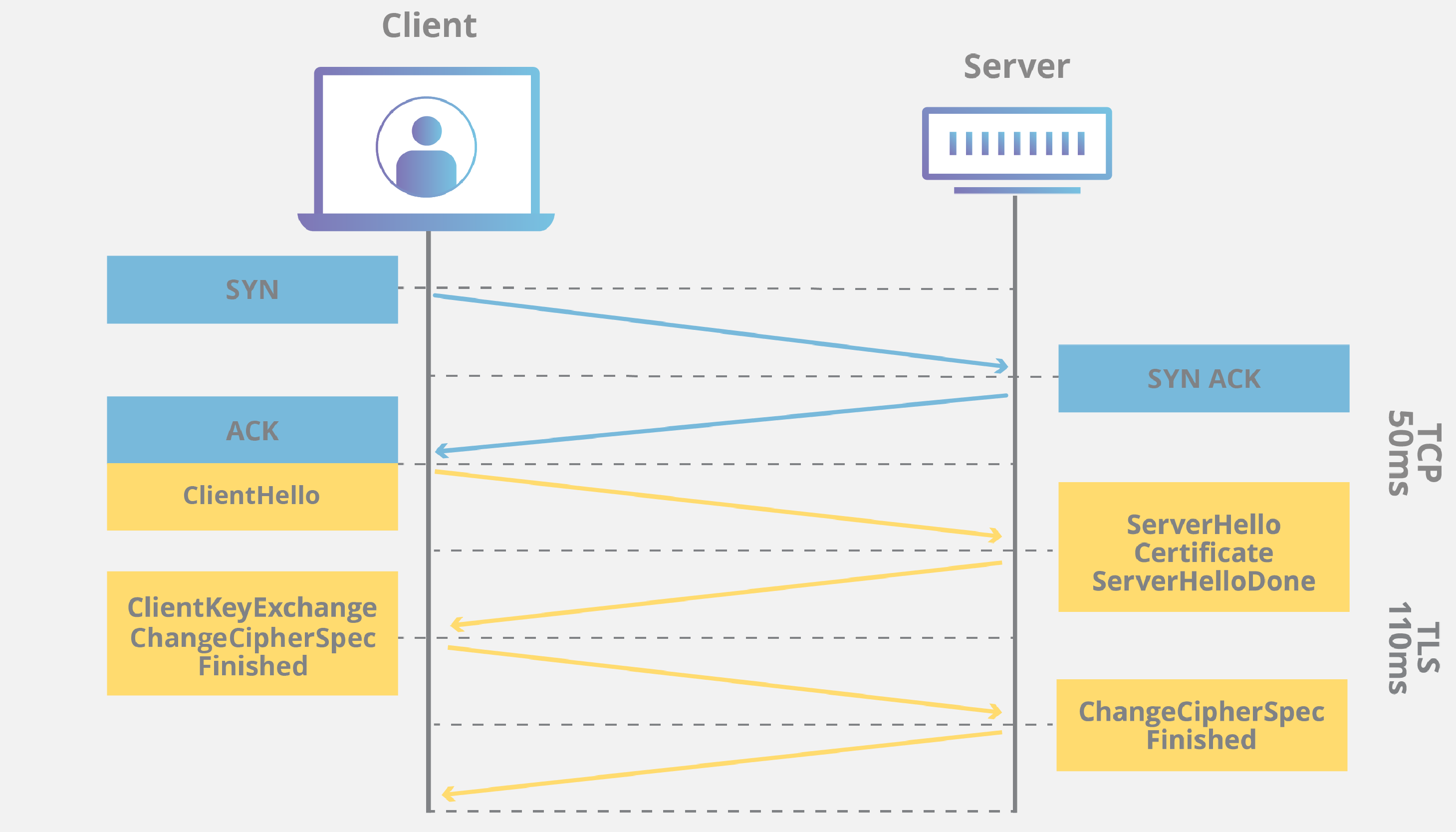
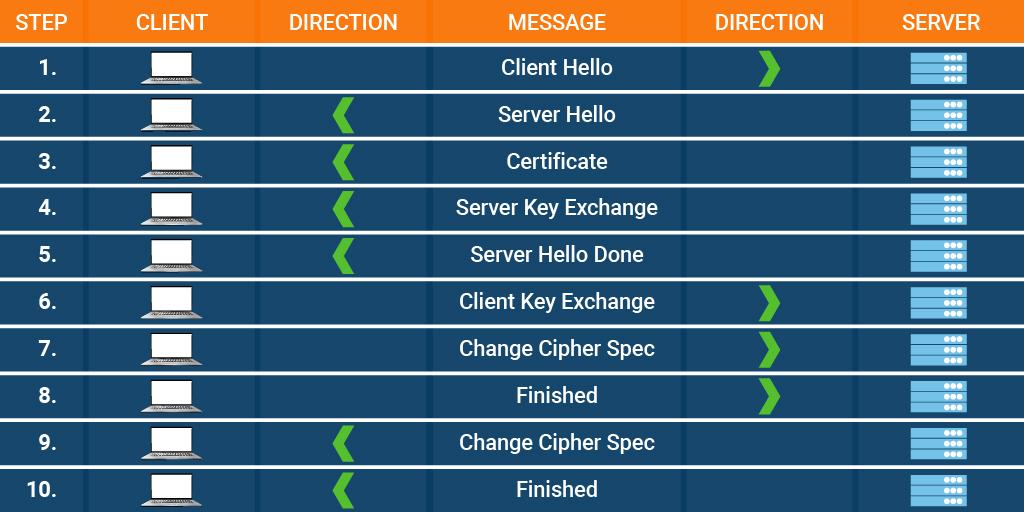
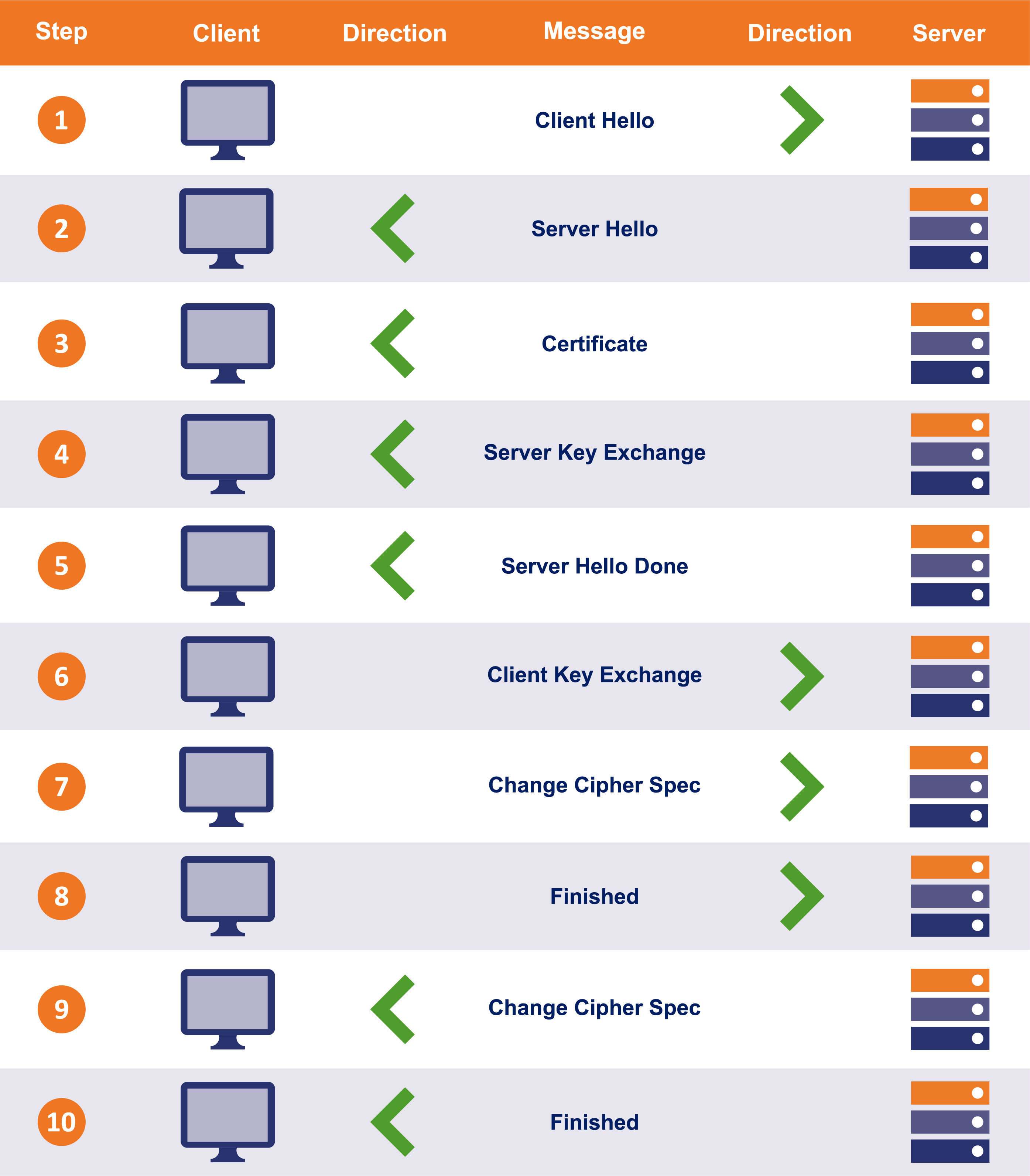
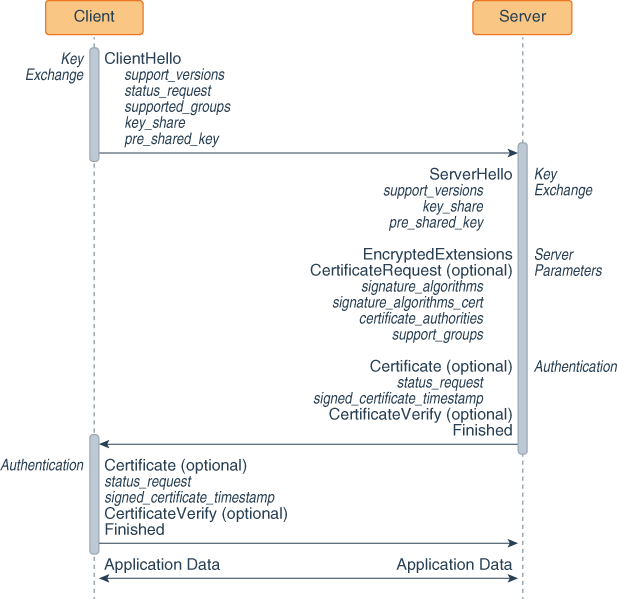
TCP and TLS handshake: What happens from typing in a URL to displaying a website? (Part 2) | by Alysa Chan | Medium

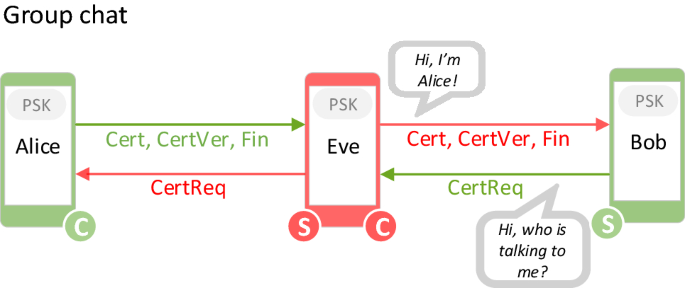
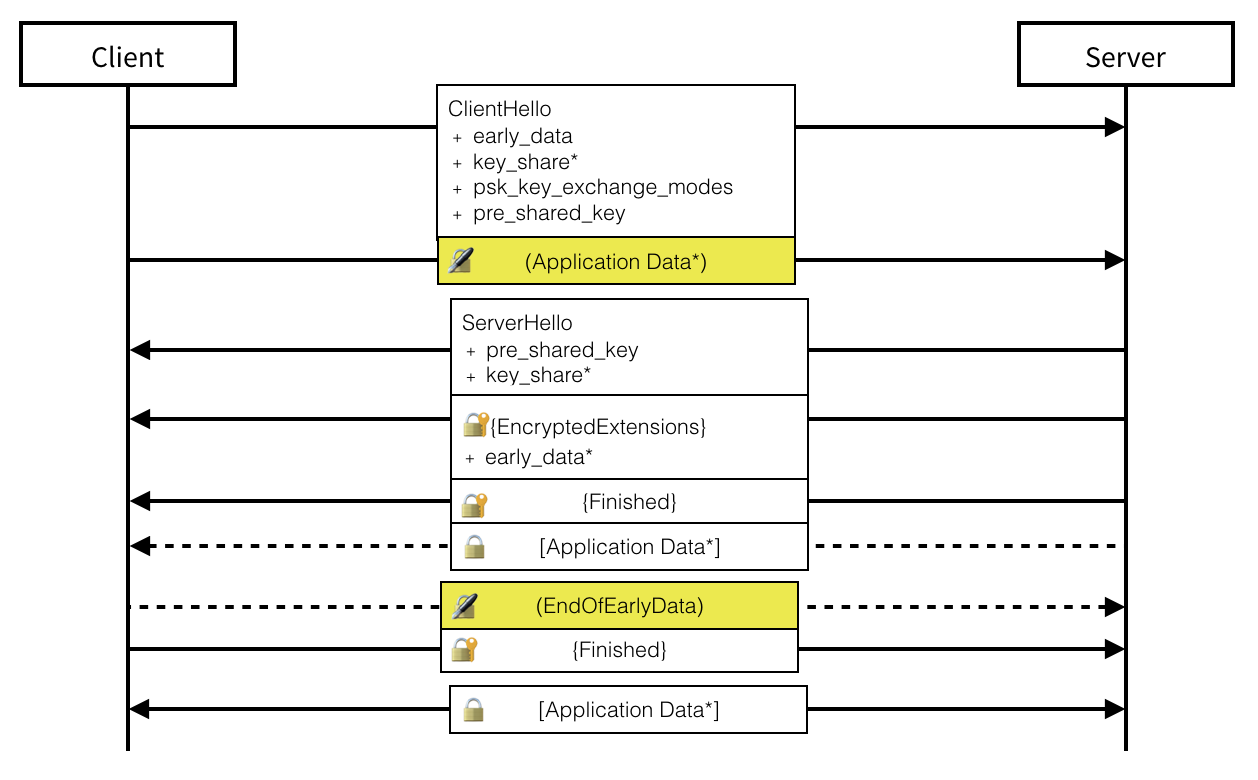
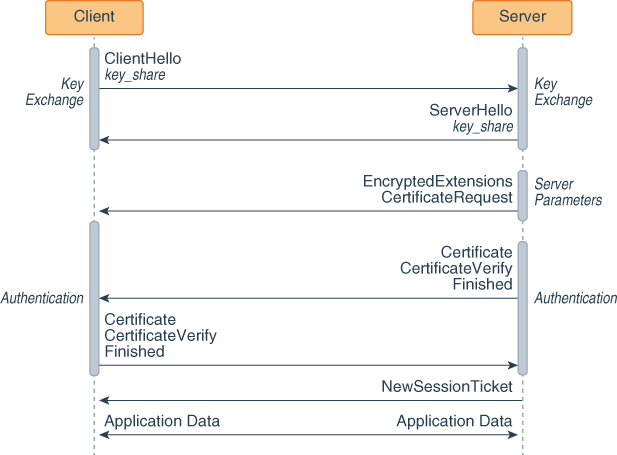
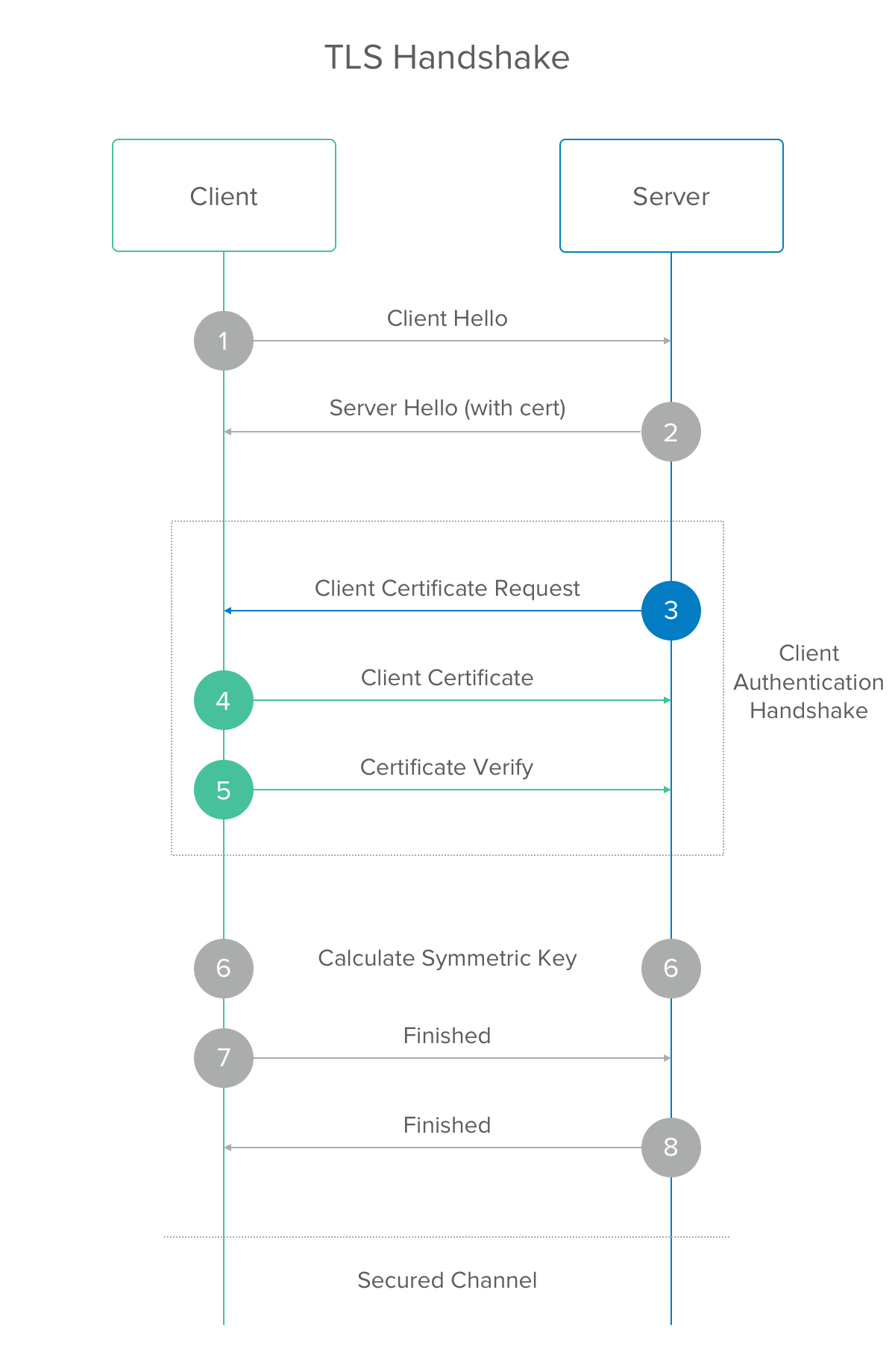
On post-handshake authentication and external PSKs in TLS 1.3 | Journal of Computer Virology and Hacking Techniques
Overview of DTLS 1.3 handshake protocol with mutual authentication and... | Download Scientific Diagram

c++ - TLSv1.3 post-handshake: server only verifies the client certificate when the connection is closed - Stack Overflow

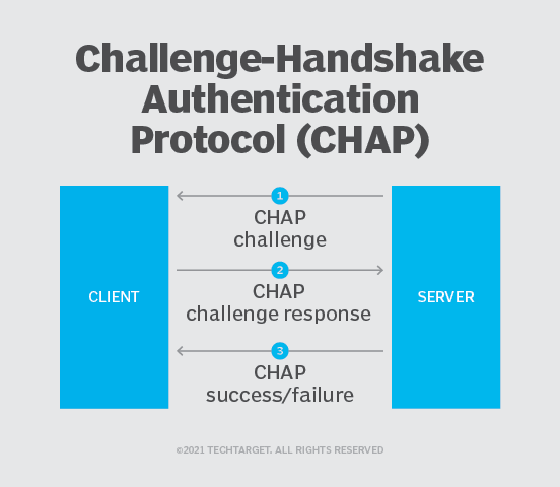
What is Challenge-Handshake Authentication Protocol (CHAP) and how does it work? - The Security Buddy

On post-handshake authentication and external PSKs in TLS 1.3 | Journal of Computer Virology and Hacking Techniques